How Does Ontology Work? A Complete Process from Identity Verification to On-Chain Trust
As blockchain applications continue to expand, simple asset transfers are no longer enough to meet complex real-world needs. Identity verification, data reliability, and multi-party collaboration have become increasingly important challenges. In traditional internet architectures, however, these capabilities typically depend on centralized platforms, which leads to data silos and higher trust costs.
Ontology offers a solution centered on decentralized identity and trust mechanisms. Its design is not built around transactions, but around the establishment of trust. By integrating identity, data, and verification processes, Ontology creates a repeatable trust framework within a decentralized environment, giving it foundational significance in the fields of digital identity and data collaboration.
Overview of Ontology’s Operational Logic
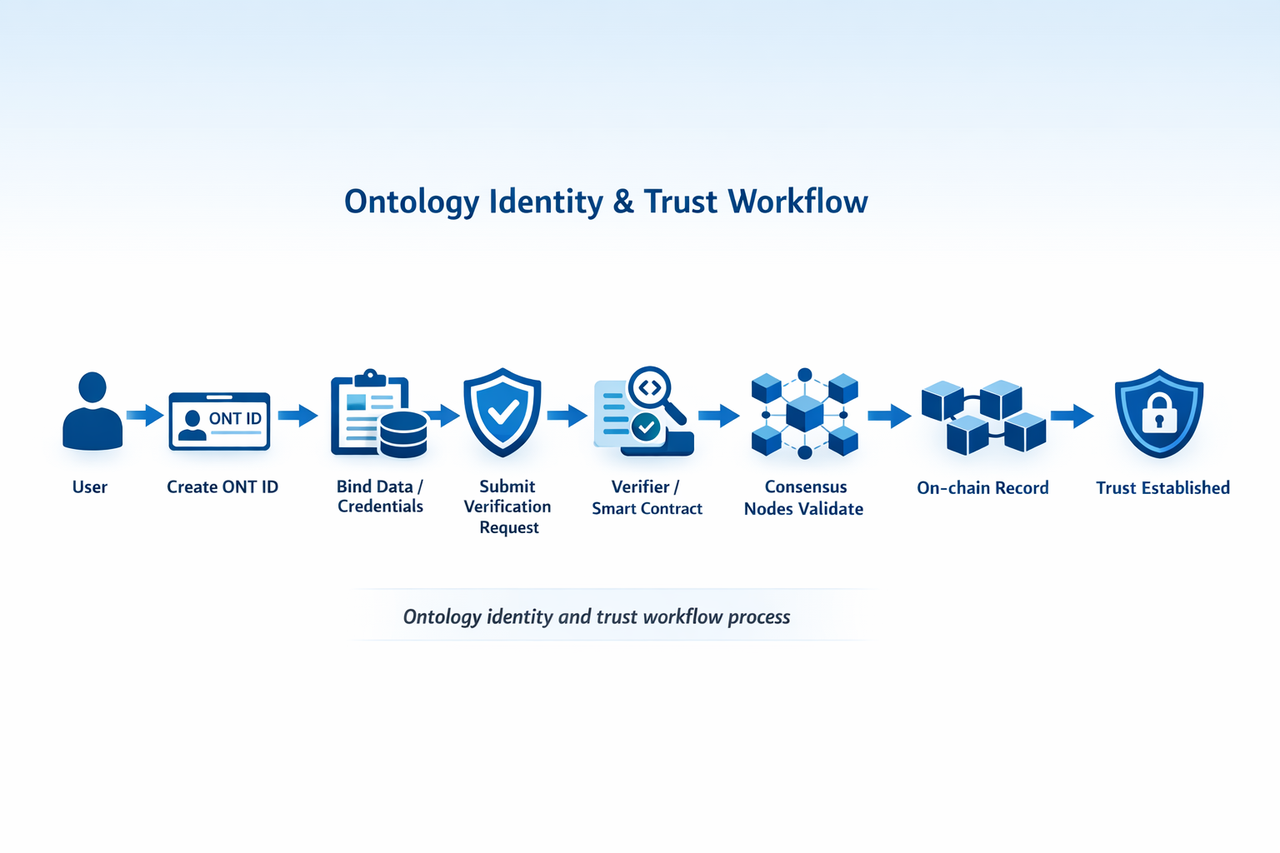
Ontology’s overall operation can be understood as a transformation from identity to trust. Multiple modules work together to convert trust relationships that once depended on third-party institutions into verifiable on-chain logic.
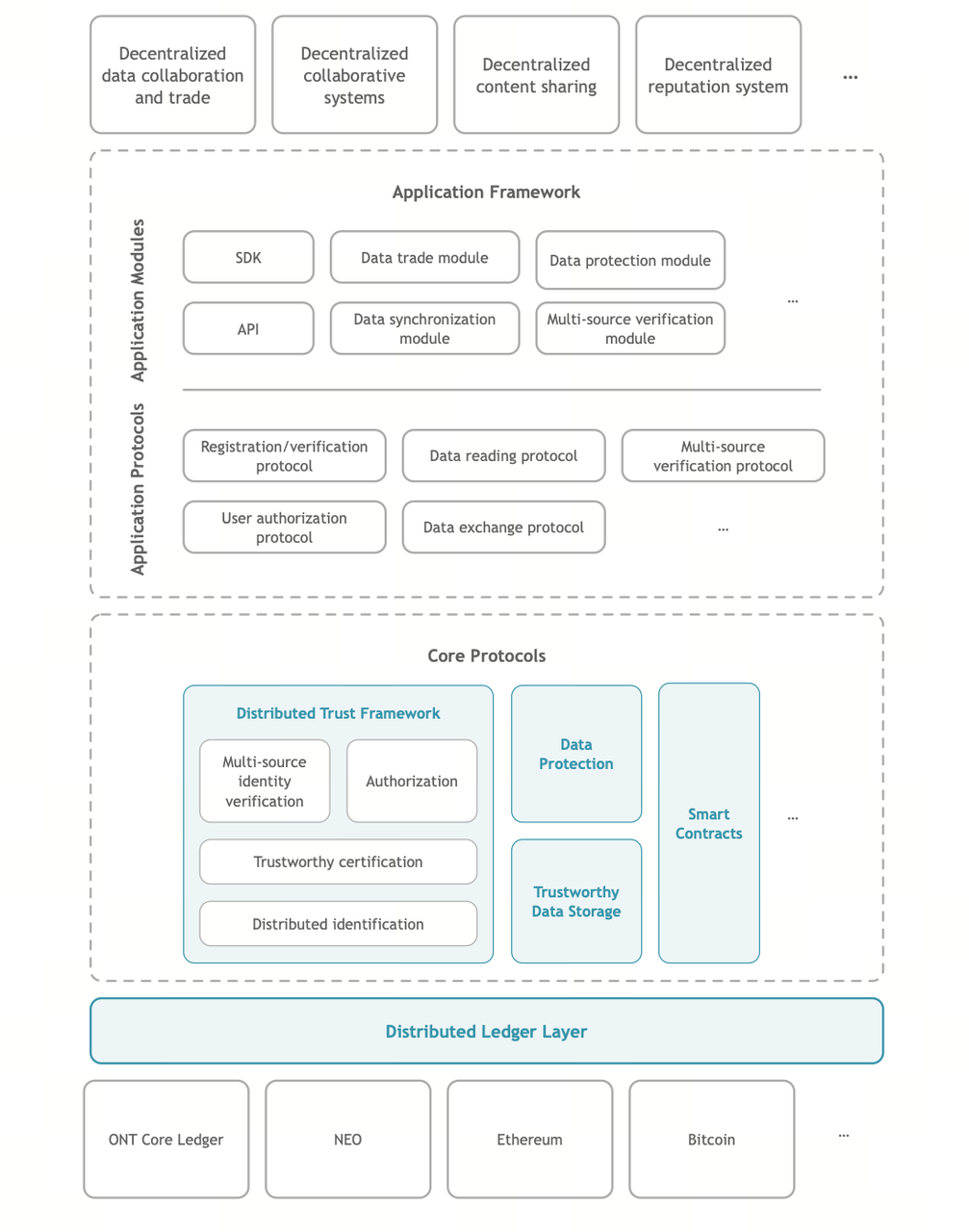 Source: Ontology White Paper
Source: Ontology White Paper
This process typically includes several key steps. Users create a decentralized identity (ONT ID) and bind data or credentials to it. When verification is needed, cryptographic signatures and credential validation are used to confirm authenticity. Finally, network nodes validate and record the results through a consensus mechanism. Together, these steps form a trust system that operates without centralized intermediaries.
How Do Users Create an ONT ID (Decentralized Identity)?
ONT ID serves as the foundation of identity within the Ontology network. Creating an ONT ID essentially involves generating a set of cryptographic keys and registering a unique identity identifier on-chain.
This process typically includes generating a public-private key pair, creating an identity identifier, and writing the relevant information onto the blockchain. Unlike traditional account systems, ONT ID is fully controlled by the user, with no reliance on centralized platforms for identity management.
This design allows users to reuse the same identity across different applications while avoiding fragmentation caused by platform differences.
How Are Identity Binding and Data Ownership Established in Ontology?
After creating an ONT ID, users can bind various types of data to their identity, such as personal information, certificates, or behavioral records. To prevent privacy leakage, Ontology generally does not store raw data directly on-chain. Instead, it records proofs of the data using hashes or credentials.
The core of data ownership lies in determining who owns the data and whether it is authentic. By linking data to an ONT ID and introducing verifiable credentials, third-party institutions can sign and certify the data, creating a trusted data source.
This mechanism ensures that data remains verifiable without being publicly exposed, laying the groundwork for future data exchange and validation.
How Is Trust Verified in Ontology?
When users need to prove their identity or data in a given scenario, Ontology’s verification mechanism comes into play. Verifiers can check whether the provided signatures and credentials come from trusted sources and whether they have been tampered with.
Trust is not established by a single authority. Instead, it is derived from a combination of factors, including identity signatures, credential issuers, and on-chain records. As long as these elements can be successfully validated, the information can be considered authentic.
This model of verifiable trust allows trust relationships to be established across multiple parties without relying on traditional centralized authentication systems.
How Does On-Chain Consensus Ensure Data Integrity?
Within the Ontology network, all critical operations must ultimately be confirmed through a consensus mechanism. Nodes are responsible for validating transactions and data, then packaging them into blocks to create tamper-resistant records.
The purpose of the consensus mechanism is to ensure that all participants in the network agree on the state of the data. Once data is written to the blockchain, it becomes traceable and resistant to modification, which strengthens the overall reliability of the system.
Through this approach, Ontology transforms trust from a matter of human judgment into a system-level guarantee, making data verification more transparent and repeatable.
The Roles of ONT and ONG in the Process
Ontology operates using a dual-token model, where ONT and ONG serve different purposes. ONT is primarily used for staking and governance, representing network participation and rights. ONG, on the other hand, is used to pay for on-chain operations.
In practice, actions such as identity creation, data submission, and verification typically require ONG as transaction fees. Meanwhile, nodes earn rewards for maintaining the network, creating a sustainable economic model.
This division of roles allows the system to maintain functional stability while balancing resource allocation and incentives.
Characteristics, Boundaries, and Risks of Ontology’s Mechanism
Ontology’s operational model is highly structured. Its main strength lies in modularly integrating identity, data, and trust. This design enables it to support a wide range of use cases and scale effectively.
However, there are also limitations. For example, the system’s effectiveness partly depends on the credibility of credential issuers. In cross-system applications, differences in standards may create compatibility challenges. Additionally, balancing privacy protection with data verifiability remains an ongoing concern in real-world use.
These factors together define the practical constraints Ontology faces when operating in real environments.
Conclusion
At its core, Ontology transforms identity information into trusted relationships. Through ONT ID, data binding, credential verification, and on-chain consensus, the system establishes a verifiable trust mechanism within a decentralized environment.
This process extends beyond identity authentication. It also provides a foundation for data collaboration and multi-party interaction, giving Ontology significant infrastructural value in the digital identity and data economy landscape.
FAQs
What is the core operational logic of Ontology?
Its core logic is to establish verifiable trust relationships on-chain through the process of identity, data, verification, and trust.
What role does ONT ID play in the process?
ONT ID acts as a decentralized identity that binds data and participates in identity verification.
Does Ontology store all data on-chain?
No. It typically records data in the form of hashes or credentials to protect privacy.
How does Ontology ensure data cannot be tampered with?
Through on-chain consensus mechanisms and cryptographic signatures, ensuring data becomes immutable once recorded.
How is ONG used in the process?
ONG is used to pay for on-chain operations, such as identity creation, data submission, and verification fees.
Related Articles

The Future of Cross-Chain Bridges: Full-Chain Interoperability Becomes Inevitable, Liquidity Bridges Will Decline

Solana Need L2s And Appchains?

Sui: How are users leveraging its speed, security, & scalability?

Navigating the Zero Knowledge Landscape

What is Tronscan and How Can You Use it in 2025?


