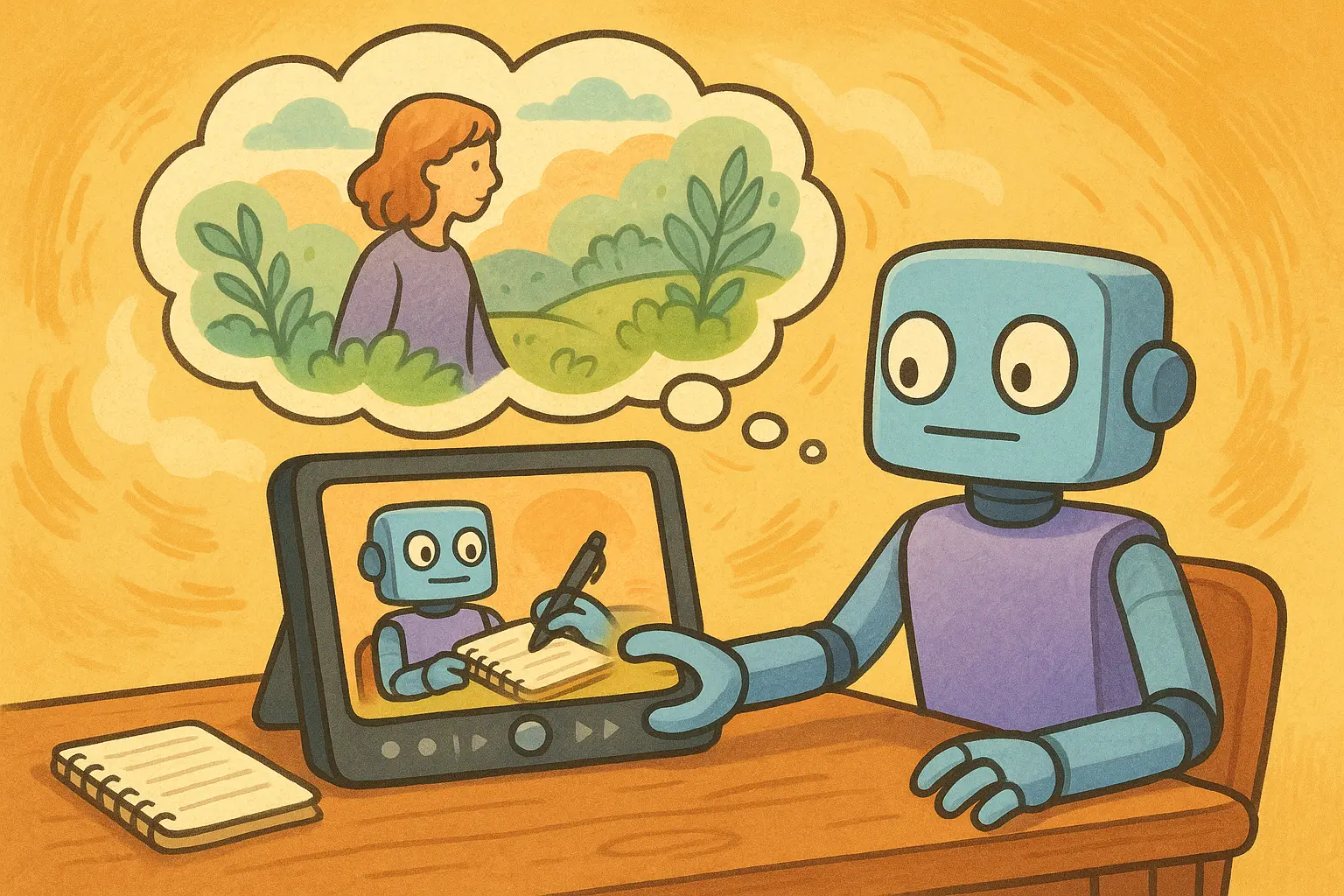
OpenClaw launches the “Dreamscapes” feature—AI agents can replay notes to build memory
OpenClaw, an open-source AI agent tool, released its 2026.4.9 version update on April 9, 2026, officially introducing the “Dreaming” feature—using a REM backfilling mechanism to process historical data, and adding a diary timeline UI so that AI agents can systematically replay users’ notes to form lasting memory. This update also strengthens security protections against SSRF and node execution injection.
“Dreaming” Feature Breakdown: How REM Backfilling Helps AI Agents Build Long-Term Memory
The “Dreaming” feature is the main highlight of this 2026.4.9 update. Its design inspiration comes from the REM (rapid eye movement) stage in biological sleep—during which the human brain organizes and consolidates daytime memories.
In OpenClaw’s implementation, the “Dreaming” feature enables AI agents to systematically replay users’ past notes and interaction logs during inactive periods. Through the REM backfilling mechanism, historical data is converted into a structured memory index, and the memory formation process of the agent is presented via the newly added diary timeline UI. This means OpenClaw agents are no longer limited to handling only the current conversation; they can also proactively turn users’ accumulated notes, preferences, and behavioral patterns into a long-term knowledge base that can be called upon for future interactions.
Overview of Key New Features in the 2026.4.9 Release
“Dreaming” Feature: Uses the REM backfilling mechanism to process historical data, allowing AI agents to replay users’ notes to form persistent memory
Diary Timeline UI: Adds a visual interface to show the agent’s memory replay and creation process
Role Tone QA Evaluation: Adds an automated evaluation mechanism for AI agent role settings and interaction quality
Android Pairing Process Optimization: Fully reworks the Android device pairing experience to improve connection stability and overall usability smoothness
Enhanced SSRF and Node Execution Injection Protection: Upgrades security protections against server-side request forgery and node code injection attacks
Security Background: Ongoing Concerns Amid Six Vulnerabilities in Two Weeks
It is worth noting that this 2026.4.9 security hardening came against the backdrop of OpenClaw recently disclosing multiple security vulnerabilities in quick succession. The earlier CVE-2026-33579 vulnerability (severity 9.8/10) was completed and patched on April 5, but this is the sixth pairing-related vulnerability revealed within six weeks for OpenClaw, all pointing to a design flaw in the same underlying authorization system.
Users currently using OpenClaw should ensure they have updated to the 2026.4.9 version and check whether abnormal pairing requests exist in activity logs. The enhancements to SSRF and node execution injection protections in this 2026.4.9 update indicate that the development team is gradually expanding the coverage of security fixes. However, whether the authorization architecture’s design issues can be fundamentally resolved remains the central question the industry continues to watch closely.
Frequently Asked Questions
How does OpenClaw’s “Dreaming” feature differ from general AI memory?
Traditional AI agents’ memory is usually limited to the context window of the current conversation. The “Dreaming” feature, however, uses the REM backfilling mechanism to let the agent systematically organize the user’s past notes during inactive periods and build a persistent memory index. This means the agent can go beyond multiple conversations, call upon earlier user preferences and behavioral patterns, and deliver a more personalized, ongoing interaction experience.
Does the security update in 2026.4.9 resolve the previously disclosed CVE-2026-33579 vulnerability?
CVE-2026-33579 was patched by the OpenClaw development team on April 5, 2026, earlier than this 2026.4.9 update. The SSRF and node execution injection protections in this release are additional security hardening measures targeting different attack vectors. All users are advised to confirm they have installed the latest version to receive all security fixes.
What practical impact does the Android pairing process optimization have on users?
This 2026.4.9 update comprehensively reworks the Android pairing process, aiming to improve pairing success rates, shorten the time required to establish connections, and enhance connection reliability in unstable network environments. For users who frequently use OpenClaw agent features on mobile devices, this will bring a noticeable improvement in the user experience.